Metasploit Community CTF 2020 (Dec)

Metasploit ran another community CTF this year, and we decided to put forward a team. The team ended up bigger than all other teams I’ve been part of before and hence PrettyBeefy team was born.
The previous Metasploit CTFs have been some of my favourites and this year did not disappoint. There were lots of very cool challenges and I have written up some of the more interesting ones:
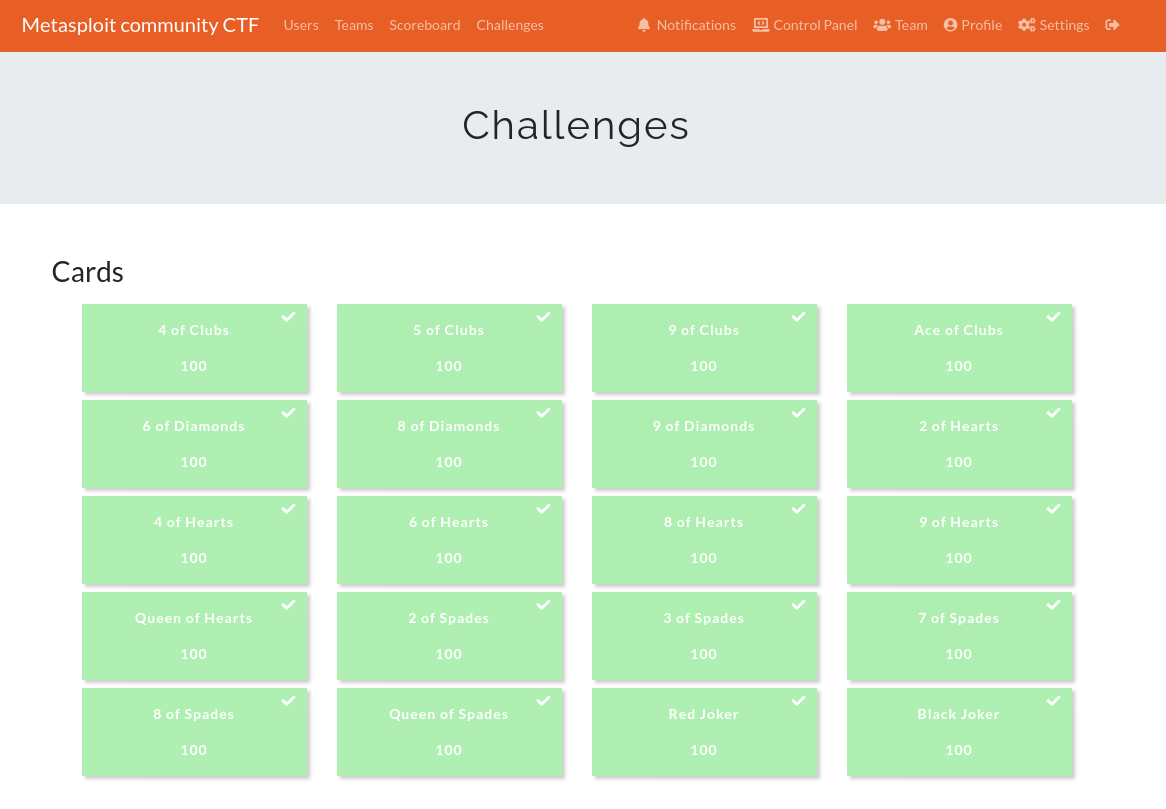
- 5 of clubs (port 8101)
- 7 of spades (port 8888)
- 9 of clubs (port 1337)
- queen of hearts (port 9008/9010)
- ace of clubs port 9009
All of the other flags have been written up by my team-mate rushi and can be found here.
As with the previous years the flags were the md5 hashes of Metasploit playing cards and this year they had a cool glitch design.
We managed to solve all of the challenges by the Saturday morning and solidified ourselves 2nd place just below a team of HTB staff members.
Unfortunately many of our team members were planning on joining in over the weekend, and we kind of ruined that for them.
The completed scoreboard
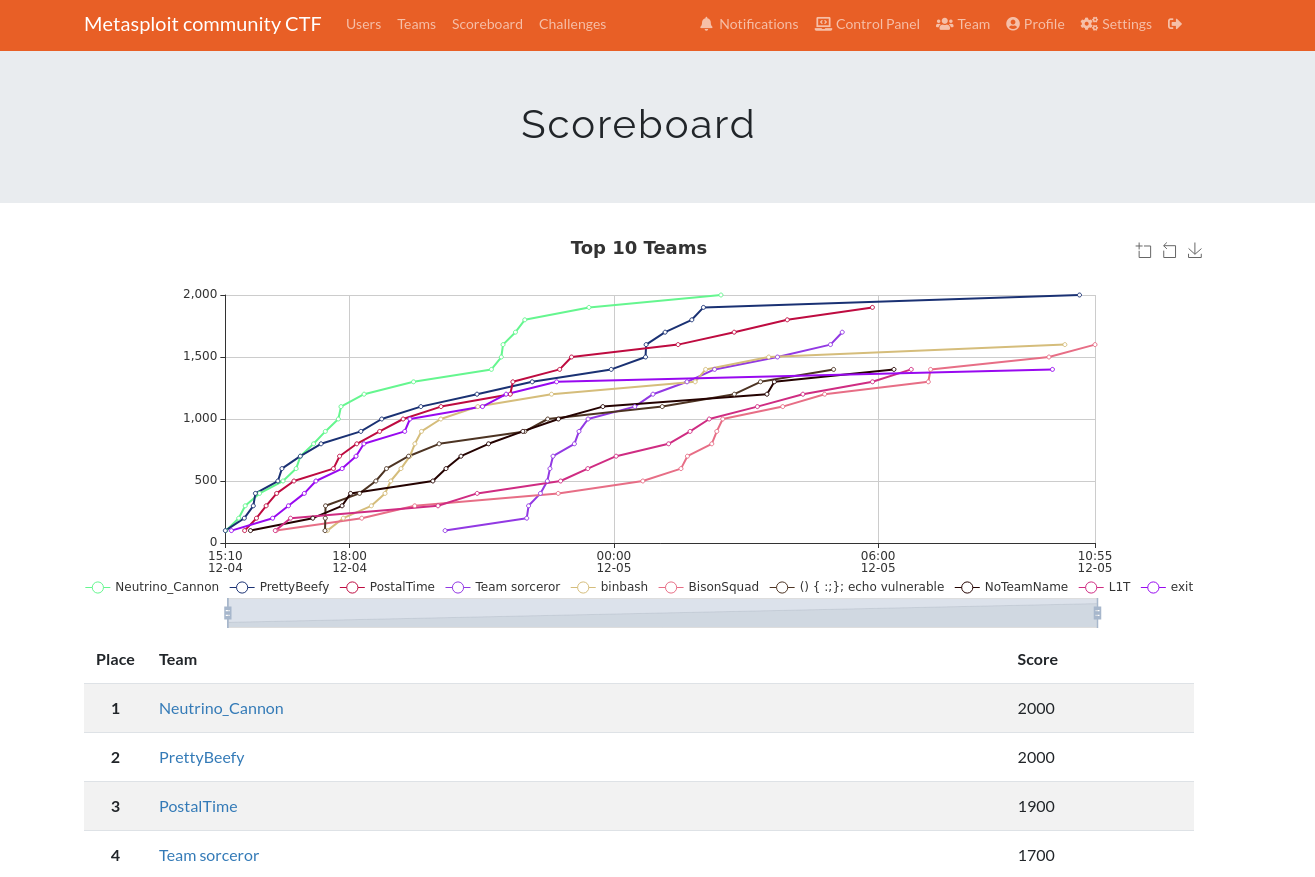
Scoreboard at time of coming in 2nd
Overall it was another great CTF, and while it was a bit easier than previous years I learned a lot and had a great laugh with the PrettyBeefy team. I’m very much looking forward to the next Metasploit CTF.
